X11 hacking is not a new concept by any means, but it’s still startlingly relevant to red team engagements on modern networks. Far too often, I’ve seen system administrators or network engineers decide they need to run Linux/Solaris/BSD as their primary desktop and don’t bother (or know how) to lock it down because it’s UNIX, it’s obviously more secure than those Windows systems. This creates a golden opportunity for us pentesters.
Looking For X11
First, scan a network looking for open X11 servers – commonly found on tcp/6000 (but could be 6001+ depending on what display they’re using). Metasploit also has an auxiliary scanner module (open_x11) to help you look for this, too. Most modern distributions disable remote X11 because it’s such a huge security issue. In fact, it can be a serious pain to figure out how to enable it depending on which distro you’re running and what window manager. That being said: Google is full of people ranting about “how do I enable remote X11?” so you’re bound to see it on client sites run by people who think they know better.
Great, so we’ve found an open X11 server. What can we do with it? Well, what can’t you do with it? Using this, we can remotely keylog, take screenshots of their desktop, watch it real-time on our machine, inject keystrokes, and so much more. This can get you the user’s credentials, information about who they are and what they’re doing, or you can just pop a terminal, run netcat, and have it connect back to your laptop.
Passive Exploitation
First up, we’ll explore some of the ways we can profit from the open X11 server without actively making any changes to their machine. Primarily, this will be used for keylogging and screenshots.
Screenshots
To begin with, we’ll take a screenshot of the remote X11 server and see if it’s actively in use or what other information we can glean from it.
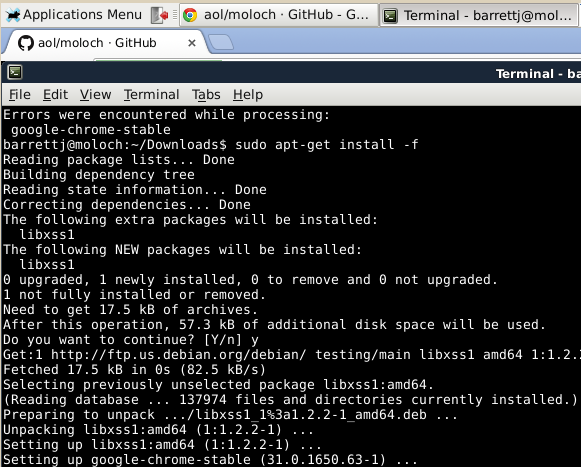
Looks like our admin installed Chrome and is now surfing Github. Is he active on the box or has he been letting it sit idle? Well, we could just repeatedly take screenshots and see if anything changes. In fact, I’ve created a script to help automate just that. But let’s be honest – you’re going to get bored if you just sit there taking screencaps.
Note: It’s entirely possible that a screensaver will be running. In that case, you can attempt to deactivate the screensaver by using xset as below. I’ve had mixed success with this on real-world networks, but occasionally you’ll get a win. Screensavers can give you some useful information (depending on how configured) including the login name of the user and the hostname.
Keylogging & Remote Viewing
Now that we know we can view what the user is up to, let’s see if we can get realtime keylogging. If you’re using Backtrack or Kali Linux, you’ll already have xspy and xwatchwin installed. If not, I found xwatchwin here and xspy here. Compiling them may be a bit of a pain, depending on distro and sources.
First, we need to gather information on the remote Xserver using xwininfo.
If you note, the window ID for the remote root window is 0x191. This will change every machine, every time you reboot as it’s dynamic. Now we can use that window ID to gather more information:
Or we can just watch the remote X display in real time to keep an eye on an admin. This is great if you’re watching him try to figure out what’s going on with his network as you’re keylogging and viewing his display. For this, we’ll need to use that window ID we found earlier.
This will create a window that lets you monitor as they work, though it can occasionally be a bit laggy on redraw.
Active Exploitation and More
Now that we’ve been spying on our lazy administrator for a while, we want to take the next step and actually get a shell on his machine. Let’s say that we saw him accessing a password file but we didn’t get to see the full contents and now we want to log in and steal it. Or we want to use his machine to pivot further into the network because he’s dual homed or on an ACL we want to bypass.
To accomplish this, tune in for part 2!
References:
- http://pipefish.me/spying-on-screens-and-keystrokes-the-dangers-of-open-x11/
- http://colesec.inventedtheinternet.com/x11-keylogger/
- http://colesec.inventedtheinternet.com/hacking-x11/
